The Office 365 Unified API at graph.microsoft.com is a nice API to work with Azure AD and Office 365 from a single API endpoint. Authorized via OAuth 2 flows and all REST/JSON etc… Pretty much as you would expect as a developer.
There are a few ways to play around with the API.
Simplest: Graph Explorer
Harder: Use a tool like Postman
Postman is pretty slick. It lets you craft HTTP requests, their headers, parameters, body etc… and get responses back formatted in various ways. Postman 3 also supports OAuth 2 flows to help simplify the process of authenticating against and API, so you dont need to do all the various hops and token copying between requests.
OAuth 2 + Postman + Office 365 unified API
Here is how it works.
1. Go install postman 3 first
2. Set up a GET request to get your profile details from Azure AD
![]()
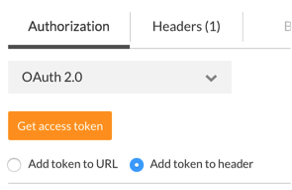
3. In the authorization area pick OAuth 2 from the dropdown
4. Next you need to go and register an app, if you haven’t already, in order to get a Client ID and Secret. There are instructions on doing that here.
Note: for the REPLY URL field you need to specify: https://www.getpostman.com/oauth2/callback
When complete make a note of the client id and secret as you will need them shortly.
5. Back in Postman enter the following details for each of the OAuth parameters:
Authorization URL: https://login.windows.net/common/oauth2/authorize?resource=https%3A%2F%2Fgraph.microsoft.com
Access Token URL: https://login.windows.net/common/oauth2/token
Client ID: (the one you got in the previous step)
Client Secret: (the one you got in the previous step)
Notice at the end of the Authorization URL you need to include the “resource” parameter. This is required with O365 and indicates what endpoint you are trying to get access to.
6. Click the “Get access token” button to initiate the authentication and authorization flow. Postman will pop up a window that will direct you to log into Office 365 and let you consent to the application being given the appropriate privileges.
When complete you will see the OAuth access token, scopes etc… that were returned.
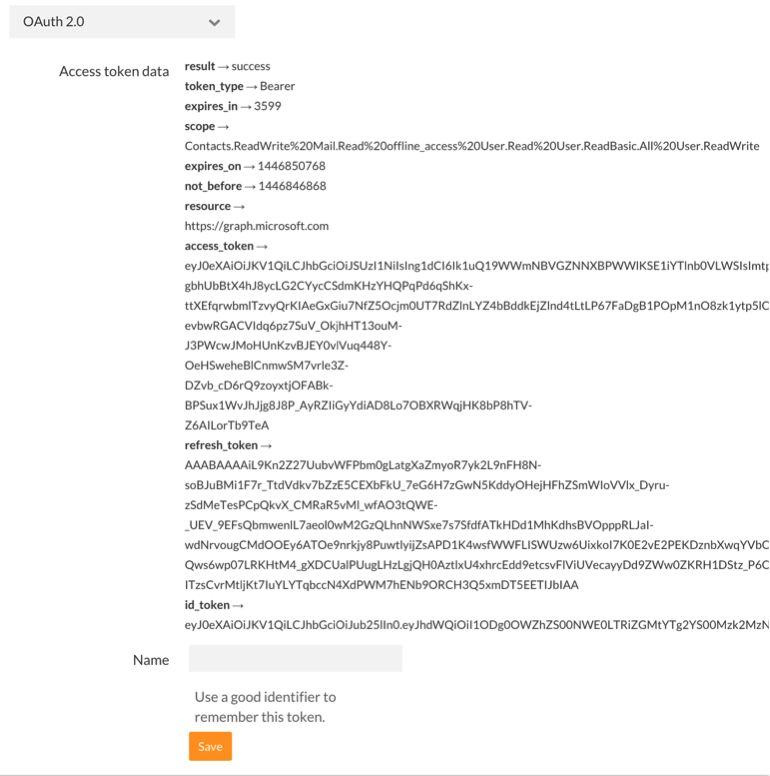
Type in a name for this token and save it. Then for all subsequent requests you can attach that token to your request like this.
1. make sure your URL is set
2. attach the token to the header of the request
3. execute the request
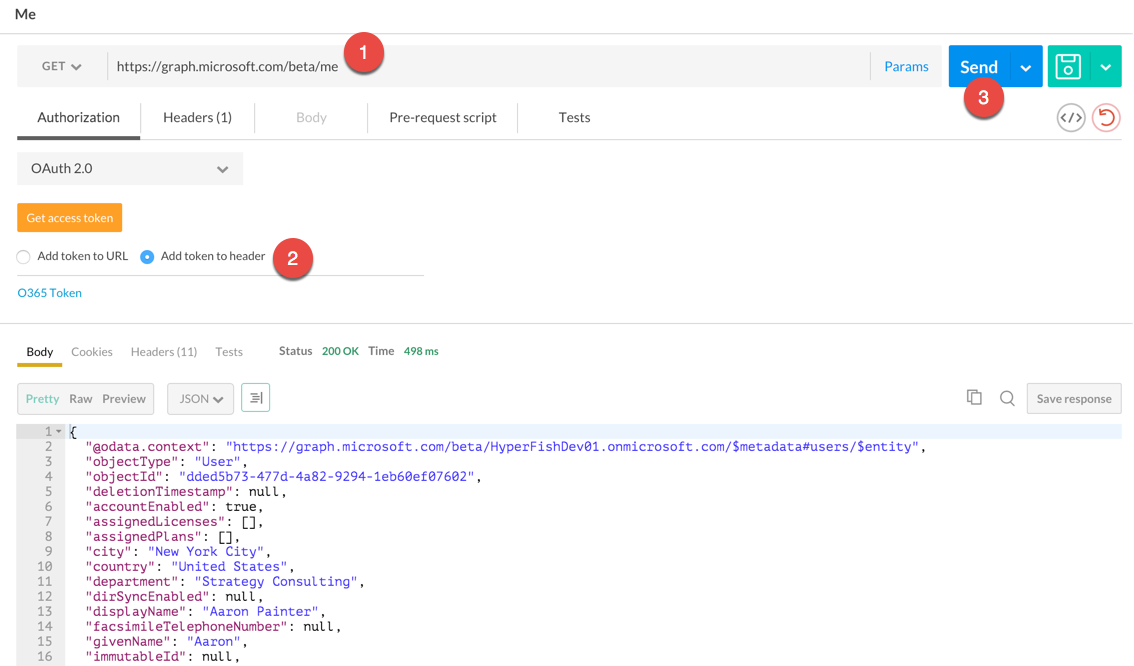
All things going well you will get back a nice JSON response with your profile information included.
Hopefully helps simplify calling the graph.microsoft.com endpoint, playing with requests and not having to deal with all the icky OAuth goo along the way.
Happy coding!

Great article Chris.
Really a helpful set of instructions to work with the APIs.
Thanks for the post. When I try to get access token, it pops up the log in page fine. But when I provide login credentials, it brings a blank page which never dismisses. I can not even see any errors. Do you know how can I go about debugging this?